by Dave Willis
Email signature management: The complete guide
15 September 2025
0 min read
TL;DR
- Email signature management is often a hidden burden for IT: manual updates, inconsistent formatting, and user error make it inefficient and frustrating
- Modern email signatures support branding, legal compliance, campaign promotion, and professionalism across all teams
- Key elements include contact info, logos, social icons, banners, disclaimers, and booking links, which all require consistency across platforms and devices
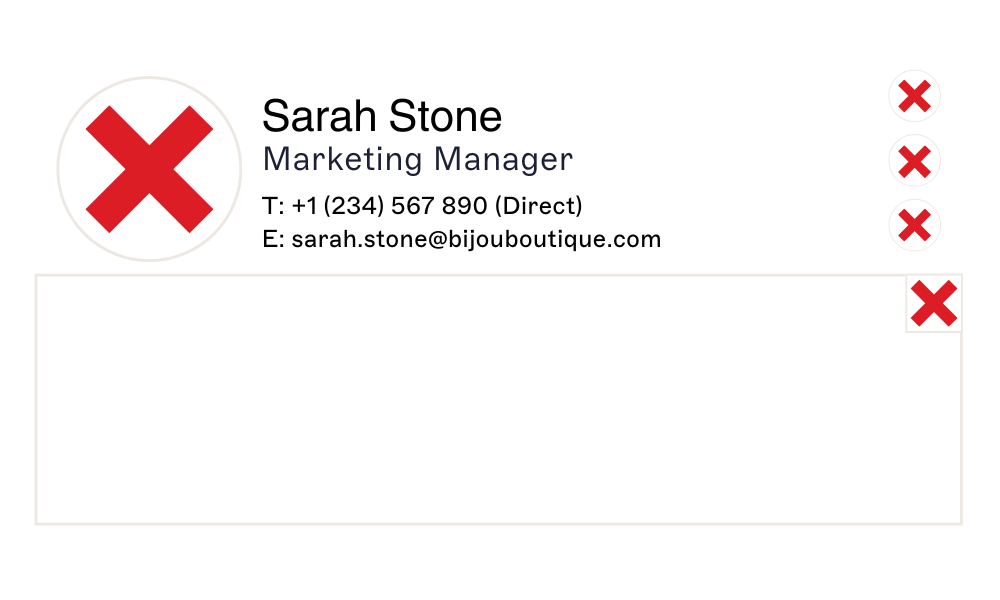
- Without a centralized email signature manager, issues like missing contact info, stacked signatures, or broken images are common
- This guide explains how to streamline, secure, and scale email signature management for modern businesses
Introduction: Why IT needs centralized control
For IT professionals, managing email signatures are rarely top of the priority list. That is until they start causing problems. Every promotion, department change, or rebrand creates another round of tickets. Employees edit their own signatures, leaving Marketing frustrated with rogue branding and Compliance worried about missing disclaimers. And when signatures aren’t applied consistently across devices, IT shoulders the blame.
cite managing and updating signatures as a top email-related drain on time and productivity.
The reality is that manual processes don’t scale. They leave IT teams firefighting formatting issues, chasing users, and managing repetitive updates that drain time better spent elsewhere. Worse, they create visibility gaps: you can’t prove what disclaimer was applied, when it was last updated, or whether mobile senders are compliant.
That’s why email signature management has become a critical IT function. A centralized email signature manager gives admins complete oversight, automates compliance, and removes the burden of manual updates.
Instead of managing signatures piecemeal, IT can enforce consistency across the entire organization — with the confidence that every message leaving the business is accurate, compliant, and on-brand.
What is email signature management?
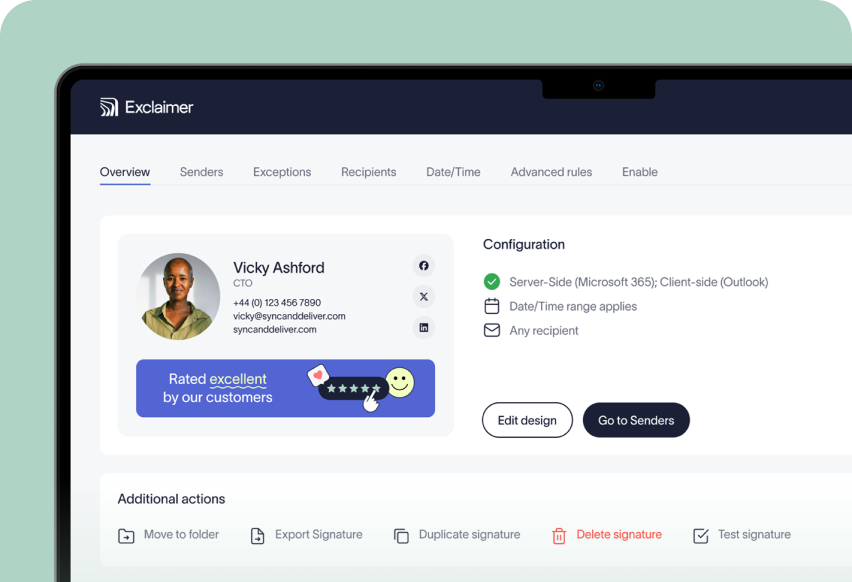
Email signature management is the process of controlling, standardizing, and automating employee email signatures across an organization. Instead of letting individual users create their own, IT uses a centralized system to apply consistent layouts, branding, and disclaimers to every email.
 A dedicated email signature manager connects directly to your directory services (like Microsoft Entra ID or Google Directory) so that user details are always accurate. When someone changes role, location, or contact information, their signature updates automatically—no tickets required.
A dedicated email signature manager connects directly to your directory services (like Microsoft Entra ID or Google Directory) so that user details are always accurate. When someone changes role, location, or contact information, their signature updates automatically—no tickets required.
Benefits of centralized email signature management
Full oversight: You know exactly what signature every employee is sending, on every device.
Automated compliance: Disclaimers are applied by rule (e.g., by department or jurisdiction) with no risk of end-user error.
Consistent branding: Logos, fonts, and formats are locked down, so Marketing doesn’t need to chase non-standard layouts.
Reduced support load: Updates roll out in minutes, not days, eliminating the repetitive admin work that clogs up IT queues.
In short, managing email signatures through a centralized platform turns a hidden IT pain into a scalable, automated process. And all aligned with your branding, security, and compliance standards.
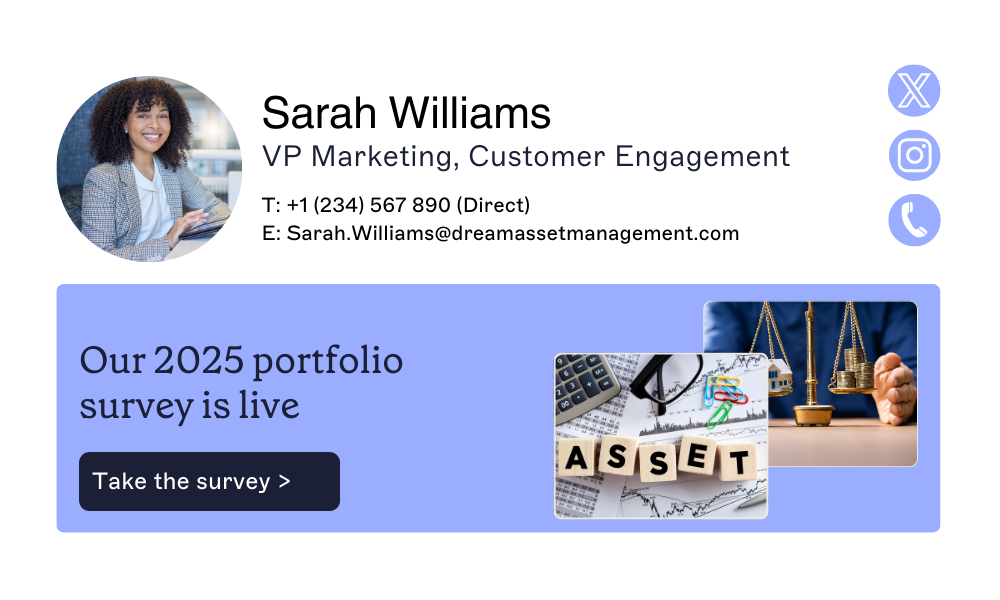
The key elements of a professional email signature
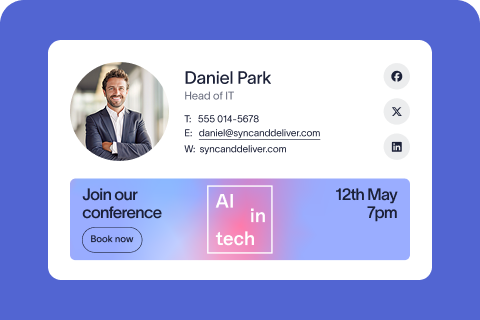
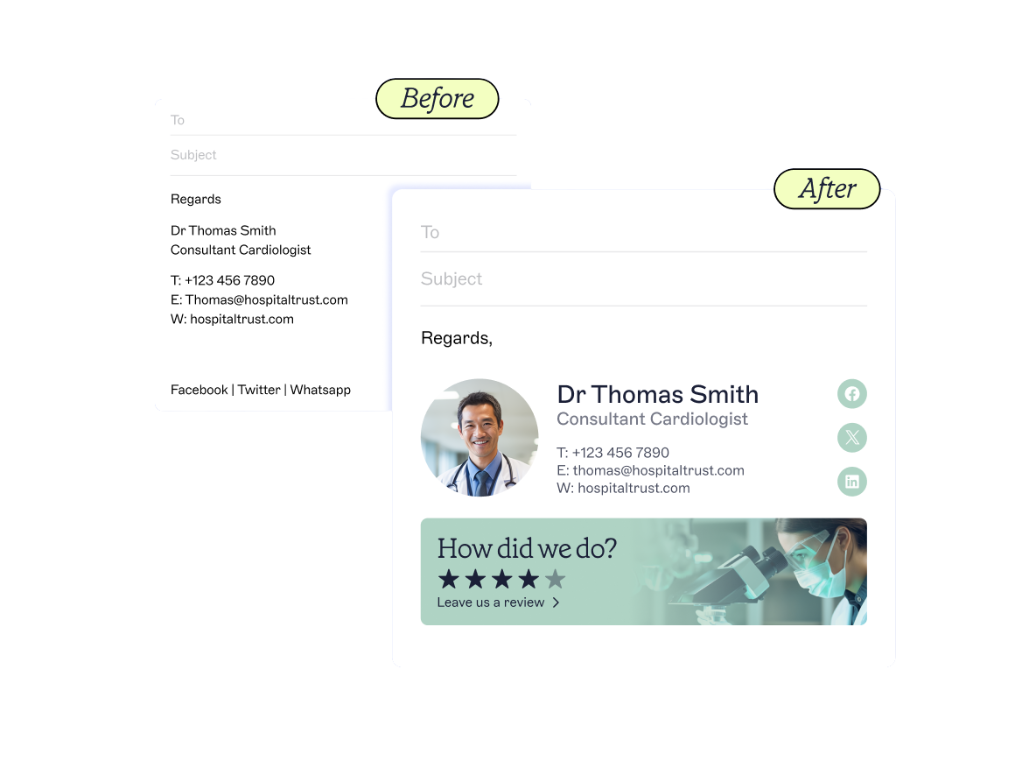
A professional email signature goes beyond simply listing your name and contact information. It should be visually appealing, easy to read, and include all the necessary elements that reflect your brand identity.
To support effective email signature management, each signature should follow a consistent layout that works across devices and platforms.
Explore best-practice layouts in our professional email signature templates guide.
1. Contact details
All email signatures are built on the contact details. These typically include your full name, job title, phone number, email address, and company website URL.
2. Branding
Beyond basic contact details, your email signature should reflect your brand identity. Incorporating your corporate logo not only reinforces brand awareness but also serves as a valuable touchpoint for engagement.
3. Promotional banners
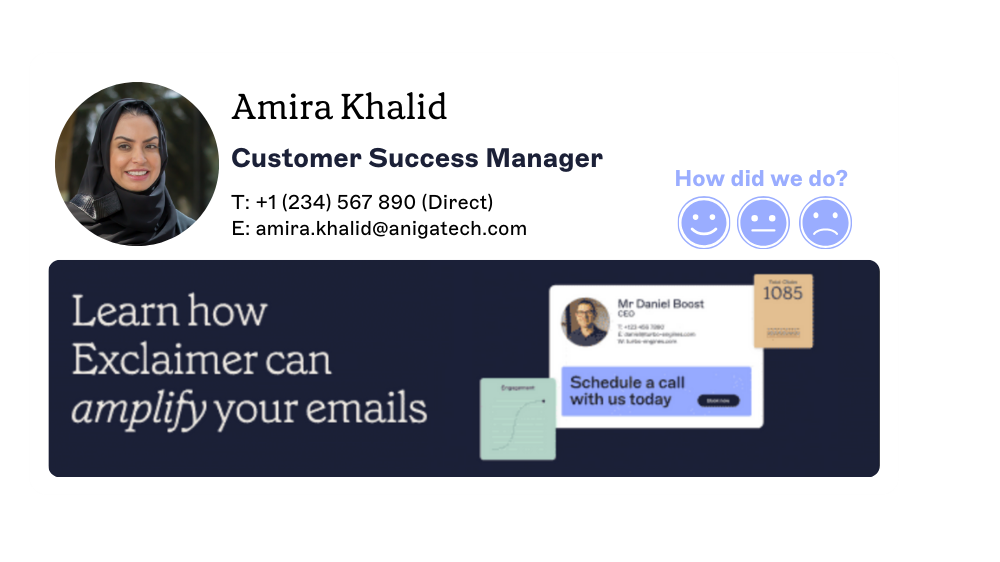
The middle section of your signature is the perfect location to display an email banner. This allows you to showcase new content, highlight special offers, or share testimonials.
4. Social media icons
Including social media icons in email signatures is an easy way to expand your social presence. This can help you gain new followers and increase the reach of your marketing campaigns as more people engage with your social media content.
5. Appointment booking link
Including calendar links in your email signature management strategy helps to streamline scheduling and enhance communication. By adding a calendar link to your email signature, people can easily book meetings or demos.
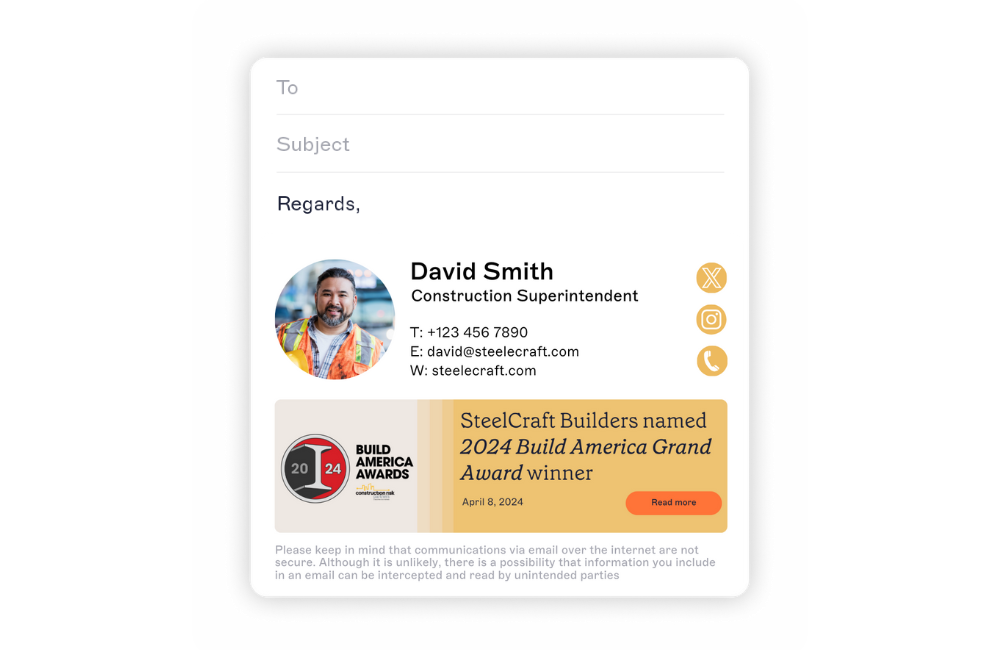
6. Email disclaimer
Email disclaimers may seem outdated, but they’re still essential for legal compliance and secure communication. The content of an email disclaimer often depends on the recipient's location and the timing of the email.
7. Company awards and certifications
Corporate certifications and industry awards can add credibility to your email signature, but only when used wisely. Including individual achievements allows employees to showcase their expertise while boosting their confidence. Similarly, highlighting industry awards lets recipients know your company has been recognized for excellence.
8. One-click feedback buttons
Your email signature can also double as a feedback channel. Adding simple, one-click rating buttons linked to an email signature survey makes it easy to measure customer satisfaction (e.g., excellent, good, average, poor).

Learn more about email signature design
| How to create an HTML email signature | Email signature format | Logos in email signatures |
| Email signature size | Email signature fonts | Reply email signatures |
9 best practices for managing email signatures at scale
To maintain a consistent and professional email signature across your organization, centralized control is essential. Typically, the IT team manages this process as they’re often the only department that has the technical ability to create uniform signatures for everyone.
 Here are nine essential best practices:
Here are nine essential best practices:
1. Create a standardized email signature template
The first step to consistency is developing a standardized email signature template for all employees.
This template should include essential contact information, as well as any required legal disclaimers or marketing banners, ensuring uniformity across your organization.Browse email signature templates that scale across teams and departments.
2. Make your email signature design simple and adaptive
When creating your company email signature, remember it will be viewed across different devices and platforms. It shouldn’t be too cluttered or complex.
Opt for a simple, clean design that highlights the essentials while leaving out unnecessary details or excessive graphics.
Learn more about creating a company email signature with examples.
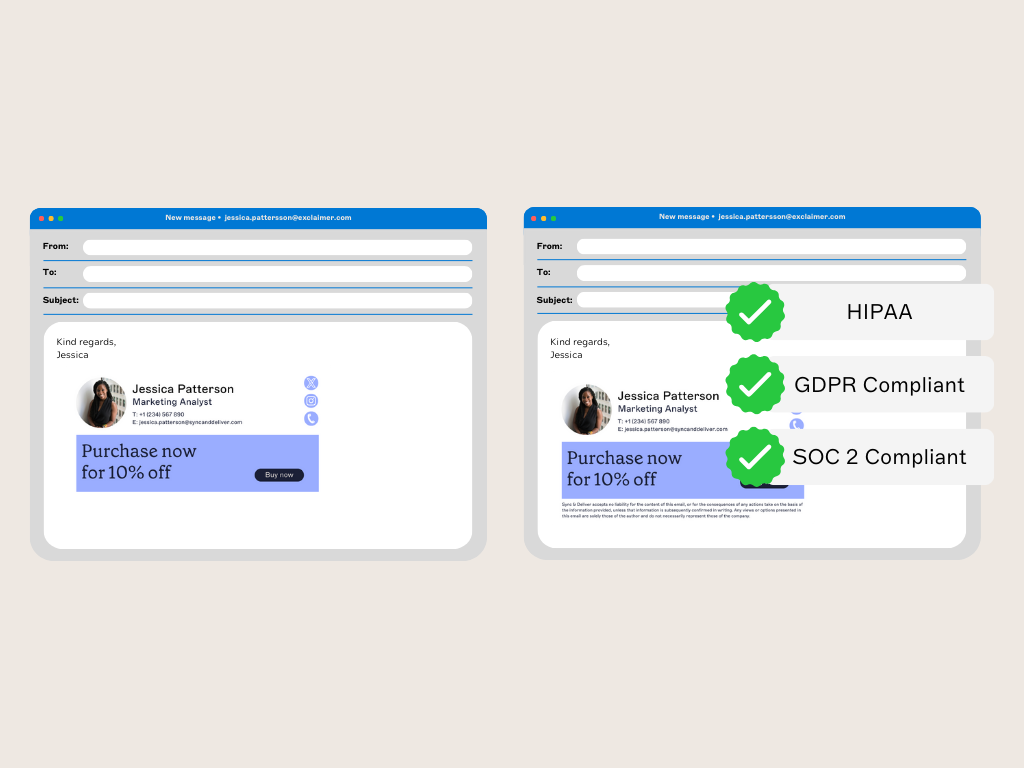
3. Ensure email signature security and compliance
Email signature security and compliance safeguards sensitive data and adheres to industry regulations.
Use secure systems to manage email signatures centrally so that employee details are protected and not tampered with. Implement encryption and secure authentication protocols to prevent unauthorized alterations or breaches.
4. Keep signatures simple for internal communication
For internal communication, use simple, minimalist email signatures without images, banners, or excessive design elements.
Streamlined signatures improve email load times and reduce visual clutter, making email threads cleaner and easier to follow.
5. Customize replies and forwards
Adding the same full signature to every reply or forward can make the thread messy and hard to read. For replies, use a simplified signature with just your name, job title, and contact information. This keeps it professional without overwhelming the recipient.
6. Test across multiple devices and platforms
Ensure your email signature HTML renders correctly by testing them on different devices, platforms, and email clients. Formatting issues can occur due to variations in screen sizes and resolutions. This means it’s crucial to verify that fonts, logos, images, and links display as intended.
7. Remember email signature size limitations
Most email clients impose size limits on attachments and embedded images. To ensure compatibility across clients, aim for an email signature under 50 KB.
Compress images and limit excessive design elements to keep within size constraints.
8. Use a web safe font
Email signatures should use web safe fonts. This ensures a consistent appearance across different email clients and platforms.
Stick to standard fonts like Arial, Verdana, Helvetica, Times New Roman, and Georgia, and avoid custom fonts that may not be supported.
9. Regularly review and update templates
Regularly reviewing and updating your email signature templates is an important yet often overlooked task. Set reminders to revisit and update your templates at least once every quarter. This is especially important after major company updates or changes in branding.
If you want to see how you get the most from your professional email signatures, get your copy of our Email Signatures for Dummies guide today.
Read nowLearn how to create an email signature by platform
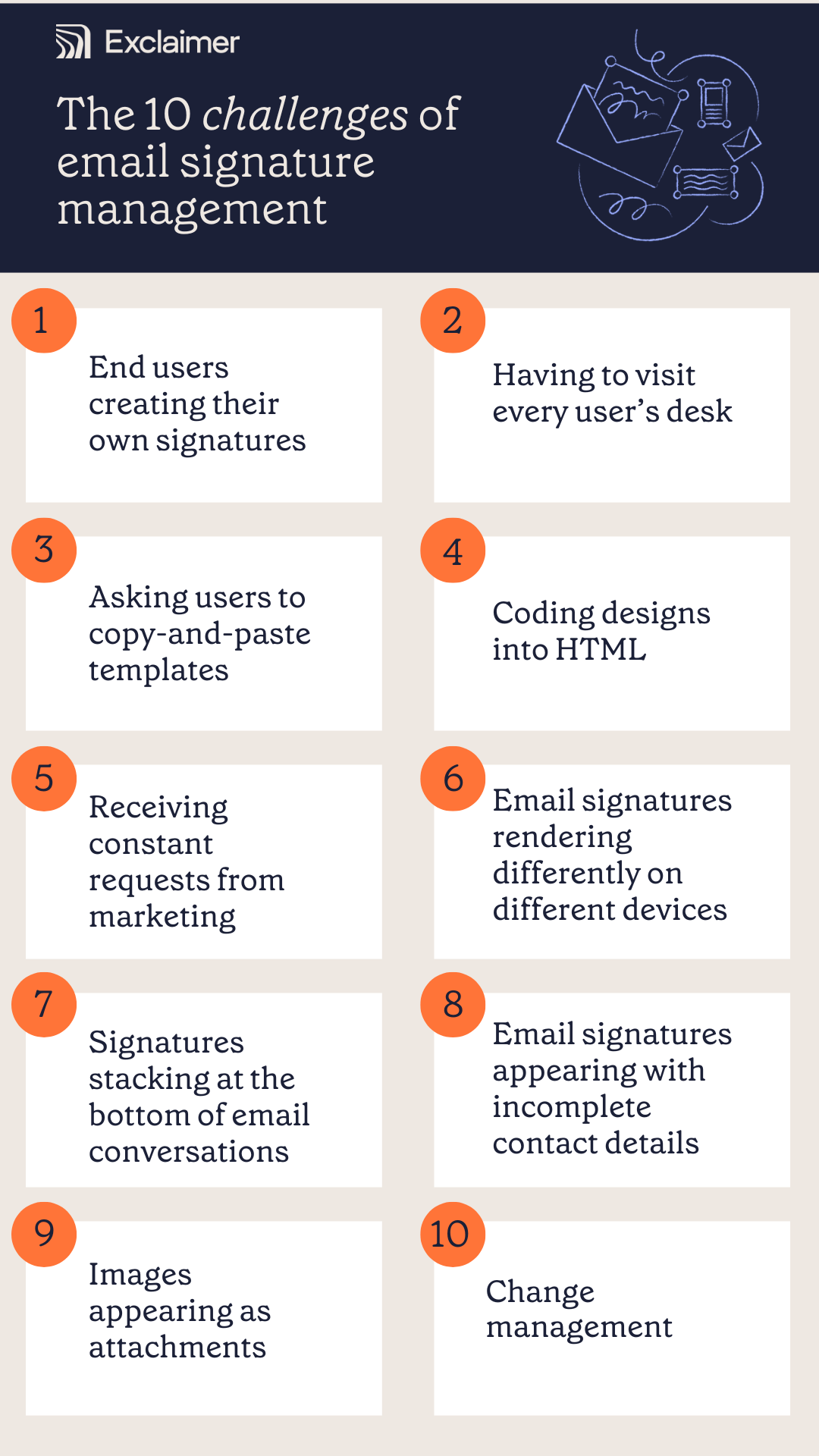
Top 10 challenges of managing email signatures
While email signatures seem simple, managing them across an entire organization creates significant complexity—especially when done manually.
 Here are the 10 most common challenges IT teams face when trying to maintain consistency, compliance, and professionalism in employee email signatures:
Here are the 10 most common challenges IT teams face when trying to maintain consistency, compliance, and professionalism in employee email signatures:
1. End users creating their own signatures
When IT end users are allowed to change their own email signatures, it can disrupt consistency and branding. Without a centralized management system, IT quickly loses control, which leads to outdated or inconsistent signatures across employee emails.
2. Having to visit every user’s desk
One outdated approach involves visiting each employee's desk to manually update email signatures. While this works for a small team, it’s not feasible for larger or remote/hybrid organizations. This often leads to inefficiencies.Did you know? Creating just one email signature template each quarter for a 100-person company can cost $9,168 a year.
3. Asking users to copy-and-paste templates
Instead of walking to every desk, IT might decide to email a signature template to everyone. This lets employees copy and paste a company-approved design into their email client. This process may seem like a quick fix, but it's not scalable.
Regularly updating signatures this way creates more work and confusion, especially with large teams.
4. Coding designs into HTML
IT can create a signature template with custom HTML, offering more control but posing challenges. On Office 365 (Microsoft 365) or Microsoft Exchange, disclaimers with HTML appear at the bottom of email chains, not under the latest message. In Google Workspace, HTML can be added via the Append footer setting, but the signature design, not raw code, must be pasted.
5. Constant requests from marketing
For marketing teams, email signatures present a valuable opportunity to expand a company’s social reach. They’re an effective way to amplify marketing campaigns. However, updates require swift action to keep campaigns on track, which end up landing on the IT team.
6. Signatures rendering differently on devices
Email signatures can look different on various devices and email clients. For example, iOS strips HTML formatting, displaying signatures in plain text. What appears perfect on a desktop might look broken on mobile devices, leading to a poor user experience.
7. Signatures stacking at the bottom of threads
Every time a user replies to a message, the signature will stack at the bottom of the conversation. This is because native email signature functionality such as the Office 365 disclaimer function focus on adding plain text to emails. These are not effective for managing HTML email signatures.
8. Incomplete contact details in signatures
Many businesses use a central directory, such as Azure Active Directory (AAD) or Google Directory. These directories auto-populate contact information in email signatures. But incomplete or missing employee contact information can lead to email signatures with gaps. This issue requires time-consuming fixes, as data discrepancies must be addressed manually. 
9. Images appearing as attachments
Images in an email signature often need to be hosted online. However, most email clients block externally hosted images by default for security reasons. If you embed images into your template by copying-and-pasting, the recipient may see a blank box with a red “X”. They might even find the image attached as a separate file.
10. Change management becomes a nightmare
Any company changes can make maintaining consistent email signatures difficult. For example, migrating IT systems, such as moving from Microsoft Exchange to Office 365, can face the challenge of rebuilding their entire signature template library from scratch.
Why native email signature tools fail at scale
While Microsoft Outlook 365 and Google Workspace offer built-in signature functionality, they weren’t designed to support enterprise-wide consistency, compliance, or automation.
When managing email signatures across hundreds or thousands of users, native tools create more problems than they solve. Here's why IT teams often replace them with dedicated platforms:
Here’s why IT teams find them inadequate:
1. No centralized control
Outlook signatures are stored locally per device, so IT has no way to enforce a standard across the business. Gmail’s “Append Footer” option applies one static template per organizational unit — with no personalization. Neither provides a unified dashboard to design, deploy, and enforce signatures across all users.
2. Inconsistent user experience across devices
Outlook signatures don’t sync reliably between desktop, web, and mobile clients. Gmail settings vary by device, and mobile signatures often default to basic text. The result: emails sent from phones frequently lack proper branding or disclaimers.
3. Limited personalization and dynamic data
Native tools can’t pull detailed attributes from Active Directory or Google Directory. That means you can’t automatically insert fields like job titles, certifications, or region-specific disclaimers. At best, you get plain text with minimal user data, far from the level of control IT needs.
4. Poor formatting and HTML support
Images often render as attachments, HTML layouts break, and signatures lose formatting in email threads. Exchange transport rules append disclaimers at the very bottom of chains, creating messy duplication instead of professional consistency.
5. No compliance enforcement
Users can remove or alter signatures in Outlook, and Gmail’s footer can be bypassed by personal settings. That means disclaimers can be edited or deleted, leaving IT unable to guarantee legal compliance.
6. Zero analytics or audit trail
Native options provide no visibility into what signature was applied, when, or how it performed. You can’t track usage, run audits, or integrate signatures into your marketing and compliance stack.
Unlike a dedicated email signature manager, native tools lack integration, scalability, and the flexibility to enforce policies across your environment.
The benefits of centralized email signature management for IT teams
A modern email signature manager eliminates the technical burden of manual updates, broken templates, and user-dependent processes — giving IT teams back their time and control.
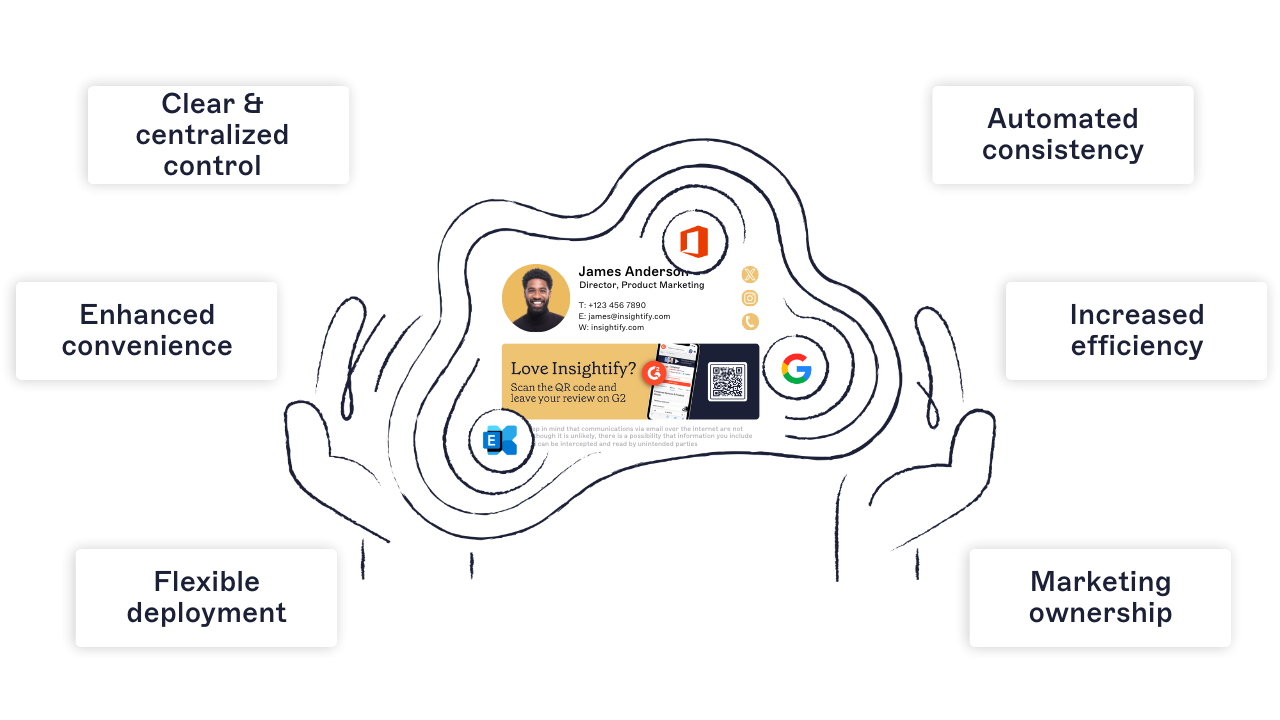 Here’s how centralized email signature management transforms daily operations:
Here’s how centralized email signature management transforms daily operations:
1. Clear and centralized control
Email signature management is automated, keeping end users out of the process. You can maintain central control over design and deployment while offering flexibility through pre-set, pre-approved templates. This ensures consistency and eliminates the need for users to make edits themselves.
2. Automated consistency
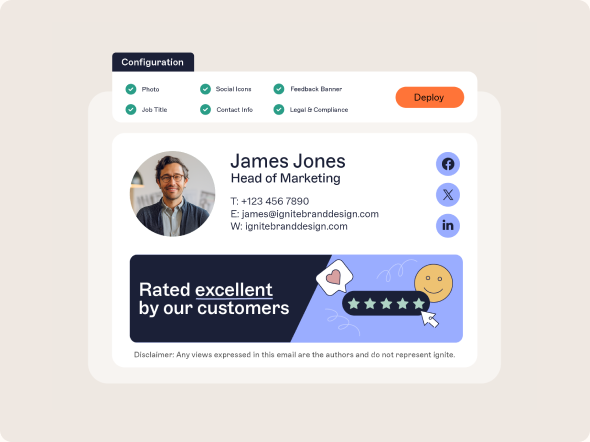
Email signature management software offers complete control and precision over a company’s email signatures. An IT administrator can preview and ensure that every detail fits perfectly before rolling it out across the organization.
3. Enhanced convenience
With a solution that allows email signature updates in just a few clicks, management becomes easy and convenient. No more starting from scratch when a signature doesn’t render or when contact details go missing.
4. Increased efficiency
By automating updates instantly, it ends common challenges like inconvenience, inconsistency, lack of flexibility, credibility issues, and human error. It's a smarter, more efficient way to manage email signatures and keeps IT's focus where it truly matters.
5. Flexible deployment
With email signature management software, IT can easily adjust details to meet a company’s needs, offering custom templates designed for specific audiences.
Before going live, all updates and enhancements can be thoroughly tested such as previewing the design, verifying hyperlinks, and conducting targeted distribution tests.
6. Marketing ownership
With a solution in place, marketing can take control of email signature management. They can design and implement email signature campaigns without creating extra work for IT.
In short, managing email signatures centrally reduces risk, improves compliance, and frees up IT to focus on more strategic initiatives.
How to implement and configure an email signature manager (step-by-step)
For IT teams managing email signatures at scale, choosing and implementing the right solution is critical to success. An enterprise-grade email signature manager should simplify creation, automate deployment, and ensure compliance across all users and platforms.
Accessibility
Ensure the platform is web-based and accessible from any location. It should support global availability, without relying on outdated on-premise solutions.
Web-based management
Centralized control dashboard
Email platform integration (Microsoft 365, Google Workspace, Exchange)
Data management
Integrate with your directory services (e.g., Azure AD, Google Directory) to ensure user data is always up to date.
Auto-fill employee details
Real-time sync and updates with no manual input
Flexibility
Your platform should allow creative freedom for Marketing and tailored control for IT.
Drag-and-drop design editor
Custom templates by department, region, or campaign
Deployment and integration
Ease of implementation is essential. Look for low-friction deployment and role-based access.
Fast setup with minimal disruption
Role-based access control for cross-team collaboration
User-friendly design
Make sure the system is accessible to non-technical users.
- One central branding hub
Accessible for HR, Marketing, and Compliance teams
Preview mode for every user group
Signature assignment
Assign specific templates to specific user groups or individual employees based on directory attributes.
Rule-based targeting
Easy visibility and audit trail for who has what
Scheduling and tracking
Plan and measure the impact of your signatures in advance.
Pre-schedule signature campaigns
Use email signature analytics to track impressions, clicks, and conversions
Security and resilience
Look for SOC 2, ISO 27001 certifications, and compliance with GDPR and other global regulations.
Encrypted data handling
Redundant cloud hosting with 99.99% uptime
Regional data processing and sovereignty controls
Did you know? Exclaimer is the only email signature management provider that holds both SOC 2 Type II and ISO certifications.
How email signature management supports branding and marketing
Even though the IT team often owns the tools, email signature management plays a major role in Marketing's ability to project brand identity and drive engagement.
 When managed centrally, email signatures provide a reliable, scalable, and measurable brand channel used in every business interaction.
When managed centrally, email signatures provide a reliable, scalable, and measurable brand channel used in every business interaction.
Here’s how a modern email signature manager supports brand and marketing goals:
1. Reinforcing brand identity
A branded email signature enhances brand perception across all communications. Elements like your logo, brand colors, typography, and tagline are important visual cues that reinforce your brand’s image
2. Creating opportunities for the marketing team
Marketers can increase ROI with email signature marketing. By adding promotional banners, CTAs, and social media icons, business emails can quickly become an engagement vehicle.
3. Improving trust and professionalism
A clean, organized signature reinforces your reliability and brand consistency to build trust that lasts. This is especially critical in legal, financial, or healthcare sectors.
4. Enhancing consistency across large teams
For organizations managing hundreds or even thousands of employees, consistency in email signatures becomes a cornerstone of brand recognition. This applies to everyone, from the CEO emailing a client to a junior team member reaching out to a vendor.
5. Measurement and analytics
Dynamic email signatures with clickable elements can also provide valuable data. Organizations can track clicks, measure customer engagement, and adjust campaigns based on performance metrics.
Did you know? 94% of marketers say that consistently branded signatures have a positive impact on email engagement rates.
How different industries use email signature management software
No matter your sector, managing email signatures at scale presents unique challenges — from legal disclaimers in regulated industries to branding consistency in distributed teams.
A centralized email signature manager solves these problems by automating signature control, improving compliance, and enabling department-level customization.
Financial services
Challenges: Missing disclaimers in trades, outdated licensing details, jurisdiction-specific disclosures.
Solution: Automated compliance enforcement for FINRA, SEC 17a-4, GDPR, and GLBA; audit-ready change tracking.
Impact: Reduced IT workload while ensuring every communication meets regulatory standards.
Legal
Challenges: Managing email signatures across practice groups, missing confidentiality disclaimers, staff making unauthorized edits.
Solution: Centralized templates with jurisdiction-based disclaimers (GDPR, HIPAA, ABA, SRA); professional, consistent layouts across all devices.
Impact: Lower compliance risk and stronger professional presentation in client-facing communications.
Construction
Challenges: Distributed teams, missing safety notices, inconsistent branding across projects.
Solution: Centralized platform with automated compliance for CDM, GDPR, and CMMC; directory sync for accurate field and HQ details.
Impact: Clear, consistent communication across job sites, offices, and contractors.
Manufacturing
Challenges: Global operations, inconsistent formatting between plants, and audit requirements.
Solution: Standardized branding across shifts and regions; audit-ready change tracking; directory sync for real-time accuracy.
Impact: Reduced IT tickets and compliance confidence during audits.
Education
Challenges: Fragmented systems, manual updates for faculty and staff, accessibility requirements.
Solution: Centralized control across campuses; support for FERPA and WCAG accessibility standards; banners for admissions or fundraising campaigns.
Impact: Fewer IT tickets and secure, compliant communication across academic and administrative units.
Public sector
Challenges: Disconnected systems, accessibility standards, lack of audit controls.
Solution: Secure, compliant signatures aligned with ADA/WCAG and FOIA requirements; U.S.-based hosting and support for data sovereignty.
Impact: Consistent branding and compliance across departments, with reduced IT overhead.
Industry-specific implementation of an email signature manager makes it easy to enforce policies, localize branding, and remain compliant without adding overhead to IT.
What’s next for email signature managers
Email remains the most widely used communication tool in the business world and managing email signatures is no longer just a compliance task. It’s becoming a strategic marketing and brand control function.
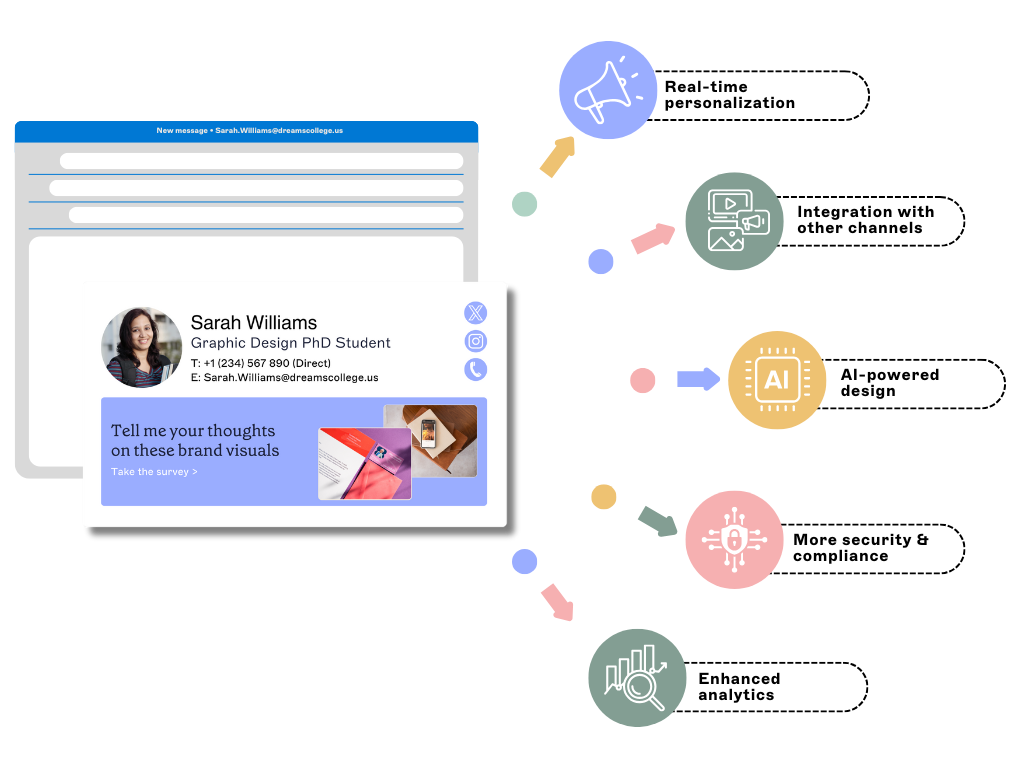 As organizations evolve, so must the tools they use. Here's what the future holds for email signature managers:
As organizations evolve, so must the tools they use. Here's what the future holds for email signature managers:
1. Real-time personalization
Personalized email signature experiences will become more prevalent. This means solutions will use real-time data to update signatures based on the recipient or sender's information.
2. Omnichannel integration
Email signature management will increasingly integrate with other communication channels. These will include CRM platforms and video conferencing tools.
3. AI-powered design suggestions
With advancements in artificial intelligence (AI), email signature management solutions may offer AI-powered design suggestions for users. This will make it easier to create professional-looking signatures without any design knowledge.
4. Enhanced compliance and security
As cybersecurity threats continue to evolve, email signature management solutions will prioritize new security and compliance features. They will offer even more security measures to protect sensitive information in email signatures.
5. Advanced analytics for ROI measurement
With the rise of big data, email signature management software will offer more enhanced analytics features. These will allow companies to track signature usage to individual users, gather valuable insights, and make more informed decisions about marketing strategies.
Forward-thinking organizations are already using AI and automation to turn email signatures into a dynamic, data-driven marketing asset—not just a static block of text.
Final thoughts: Why managing email signatures centrally just makes sense
Email is still the main way organizations communicate and isn’t going away anytime soon. Professional email signatures are important because they’re more than just electronic business cards—they represent your brand.
 But updating email signatures is a tedious and time-consuming task that places a significant burden on IT administrators. Common issues occur from signatures appearing at the bottom of email chains to images not displaying correctly have plagued IT for years.
But updating email signatures is a tedious and time-consuming task that places a significant burden on IT administrators. Common issues occur from signatures appearing at the bottom of email chains to images not displaying correctly have plagued IT for years.
A centralized email signature manager ensures:
Every signature is accurate, compliant, and consistently branded
No more manual updates or IT tickets for formatting issues
Marketing can run campaigns without sending additional emails
Legal and compliance teams can enforce disclaimers across all users
Admins have full visibility and audit control
Whether you're planning a rebrand, launching a new product, or just tired of chasing inconsistent signatures, a professional platform removes the guesswork.
💡 That’s why IT leaders at thousands of companies trust Exclaimer to simplify, secure, and scale their email signature management — across Microsoft 365, Google Workspace, and hybrid environments.
Ready to see it in action?
Try Exclaimer free and take the pain out of managing email signatures.