by Dave Willis
How to navigate the complex landscape of IT compliance
24 May 2023
0 min read
As businesses become more dependent on technology to deliver their services and products, they must contend with an increasingly complex regulatory environment.
Therefore, they must ensure their IT systems and processes adhere to relevant standards, regulations, and best practices. Compliance is essential not only for avoiding costly fines and legal liabilities, but also for maintaining customer and stakeholder trust.
This blog provides an overview for any IT professional seeking to navigate the complex world of IT compliance.
What is IT compliance and why is it necessary?
IT compliance involves three key areas.
1. The process of meeting third-party requirements
IT compliance refers to an organization's ability to meet third-party rules related to its systems and processes. These encompass IT security, data protection, availability, and integrity.
2. Establishing a GRC framework
Governance, Risk, and Compliance (GRC) is a unified approach that helps organizations align their IT strategies with business goals, manage risks effectively, and ensure compliance with industry and government regulations.
3. Regular testing by external parties
Regular testing by external parties is a crucial part of IT compliance, as it helps organizations validate the effectiveness of the controls they have implemented.
The difference between IT compliance and IT security
While IT compliance and IT security may seem similar at first glance, they serve distinct purposes within an organization.
IT security focuses on implementing effective controls to safeguard an organization's data and infrastructure. The primary goal is to ensure the confidentiality and integrity of information while preventing unauthorized access, disclosure, or modification.
In contrast, IT compliance involves applying IT security practices to fulfill external regulatory or contractual requirements.
Common IT compliance regulations
Let’s dig into the most common compliance regulations. One or more of these will likely apply to your business, so it’s worth ensuring you understand their requirements.
General Data Protection Regulation (GDPR)
The General Data Protection Regulation (GDPR), effective since May 2018, is an EU legislation governing the collection, processing, and protection of EU residents' personal data. GDPR aims to strengthen individuals’ privacy rights with safeguards over how companies collect and manage users’ personal data. Several high-profile corporations like Facebook and Amazon have been hit with severe fines for violating GDPR.
California Consumer Privacy Act (CCPA)
The California Consumer Privacy Act (CCPA) empowers Californians to access, request deletion of, and opt-out of third-party sharing of their personal data collected by for-profit companies.
Health Insurance Portability and Accountability Act (HIPAA)
The Health Insurance Portability and Accountability Act (HIPAA) is a mandatory U.S. law regulated by HHS and enforced by OCR that governs the use and disclosure of protected health information (PHI).
Sarbanes-Oxley (SOX)
The Sarbanes-Oxley Act (SOX), a U.S. law, promotes investor protection via enhanced transparency and accurate financial reporting for publicly traded companies. It mandates CEOs and CFOs' accountability, formal data security policies, and yearly audits, focusing on areas like security, data backup, and change management.
Federal Information Security Management Act (FISMA)
The Federal Information Security Management Act (FISMA) is another U.S. law that outlines guidelines and standards for protecting government data and operations.
Gramm-Leach-Bliley Act (GLBA)
The Gramm-Leach-Bliley Act (GLBA) is a federal law requiring financial institutions operating in the U.S. to safeguard and explain how they share customers' private information.
Why does IT compliance matter?
Organizations that put IT compliance at the heart of what they do can effectively protect sensitive data, prevent unauthorized access, and mitigate potential cyber threats. Creating a unified security framework also allows organizations to better identify gaps in their existing IT programs.
What’s more, demonstrating service reliability and availability bolsters companies’ reputations and helps them garner new business from security-minded customers.
The consequences of non-compliance
Failing to prioritize trust and compliance can have significant consequences, including:
Loss of customer trust: Customers won’t trust organizations that fail to protect their data, resulting in lost business and diminished loyalty
Reputational damage: Non-compliance can damage an organization's image, making it difficult to attract new customers and maintain positive relationships with existing ones.
Potential legal and financial ramifications: Ignoring regulations and industry standards can result in fines and legal action, which can be costly and damaging to an organization's bottom line.
The growing importance of cloud security standards
Organizations are increasingly transitioning to the cloud. Cloud security standards ensure that cloud service providers (CSPs) adhere to best practices for safeguarding sensitive data, preserving privacy, and complying with relevant regulations.
Ensure your company partners with vendors that comply with these cloud security standards:
How Exclaimer’s email signature management solution safeguards IT compliance
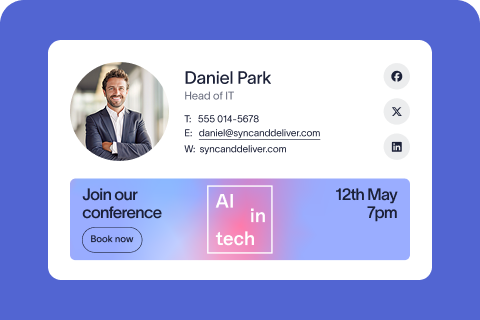
IT compliance regulations often require organizations to include specific legal disclaimers and confidentiality notices in their corporate email signatures.
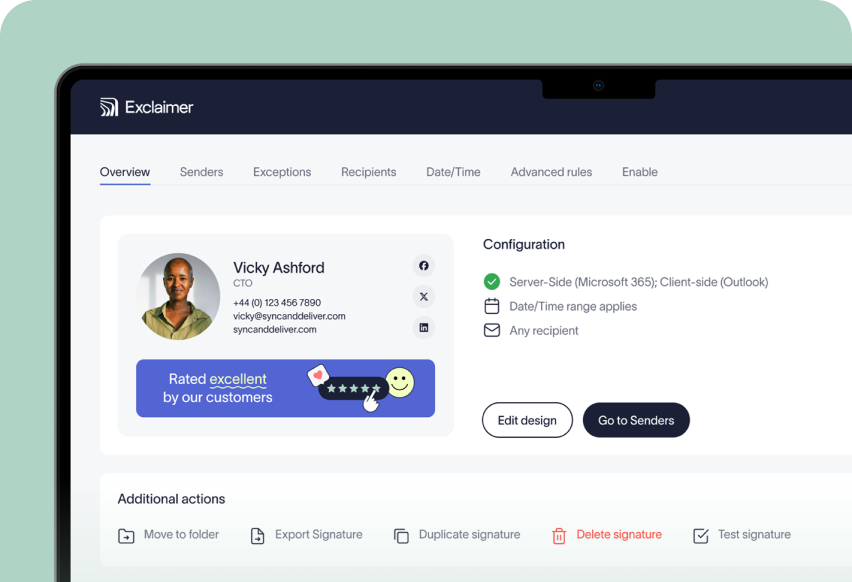
Exclaimer’s email signature management solution aids IT compliance by providing a centralized platform for managing email signatures across an organization. It allows administrators to set standardized email signature templates and policies, ensuring all employees use consistent and compliant signatures.
Additionally, Exclaimer prevents unauthorized changes being made to email signatures, which could potentially lead to compliance violations.
The final word
IT compliance is essential in today's digital landscape. Increasingly tech-dependent organizations must ensure their IT systems and processes adhere to the relevant standards, regulations, and best practices. The costs of non-compliance are steep, whether fines, loss of sensitive data, or loss of trust.
One key strategy for maintaining and achieving IT compliance is partnering with third-party vendors who share your organization's commitment to data security and regulatory adherence. Exclaimer’s email signature software is an excellent example of a solution designed to simplify compliance efforts while enhancing your organization's overall security credentials.
To learn more about IT compliance, read our comprehensive guide, Navigating the Complex Landscape of IT Compliance: A Guide for IT Professionals.
Then, sign up for a free trial of our email signature management solution to bolster your organization’s IT compliance credentials.