Security measures
These technical and organisational measures describe the security and governance controls implemented by Exclaimer to protect Personal Data processed through use by its customers of its subscription services (Customer Data).
For the purposes of Article 32 UK GDPR, EU GDPR, and equivalent data protection legislation, these measures demonstrate that Exclaimer:
implements appropriate technical and organisational safeguards
protects Customer Data against accidental or unlawful destruction, loss, alteration, unauthorised disclosure, or access
maintains the confidentiality, integrity, availability, and resilience of processing systems
maintains appropriate governance, risk management, and oversight
ensures appropriate controls relating to data residency and regional processing
These measures reflect Exclaimer’s certified Information Security Management System (ISMS) and independently audited control environment.
Further information regarding Exclaimer’s security posture, certifications, and whitepapers is available at: https://trust.exclaimer.com (registration required)
1. Governance and Organisational Security
Information Security Management System
Exclaimer maintains a documented Information Security Management System certified to ISO/IEC 27001:2022 and ISO/IEC 27018:2019. The ISMS defines security governance, risk management processes, control objectives, monitoring mechanisms, and continuous improvement procedures.
Independent Assurance
Exclaimer undergoes annual independent SOC 2 Type II audits covering Security, Availability, and Confidentiality trust principles.
Policies and Risk Management
Exclaimer maintains a comprehensive suite of documented information security, data protection, operational, and governance policies supporting its ISMS. These policies address, among other areas:
information security governance
risk management
access control and identity management
cryptography and key management
secure development and change management
incident management and breach response
business continuity and disaster recovery
vendor and supplier risk management
data protection and GDPR compliance
employee security and confidentiality
Information security and data protection risks are formally identified, assessed, and treated through a structured risk management process, with oversight by senior management.
2. Data Residency, Regionality, and Customer Control
Customer-Selected Data Region
Exclaimer provides regional hosting options. Customers select their data region at the time of service provisioning. Customer Data processed by the subscription services is processed within the region selected by the customer.
Regional Processing
Exclaimer’s infrastructure is deployed in regionally segmented cloud environments designed to support data residency commitments in respect of Customer Data.
Customer Data remains within the selected region as part of normal service operation, subject only to:
customer-initiated configuration choices
applicable legal requirements
limited, controlled access required for authorised support or security purposes under appropriate safeguards
Exclaimer does not unilaterally relocate Customer Data across regions. Any change to a region where Customer Data is processed for a customer would be made in conjunction with that customer.
Customer Sovereignty and Control
Customers retain control over the region in which Customer Data is processed and may select or migrate regions in accordance with available service options.
3. Data Processing Architecture and Storage Transparency
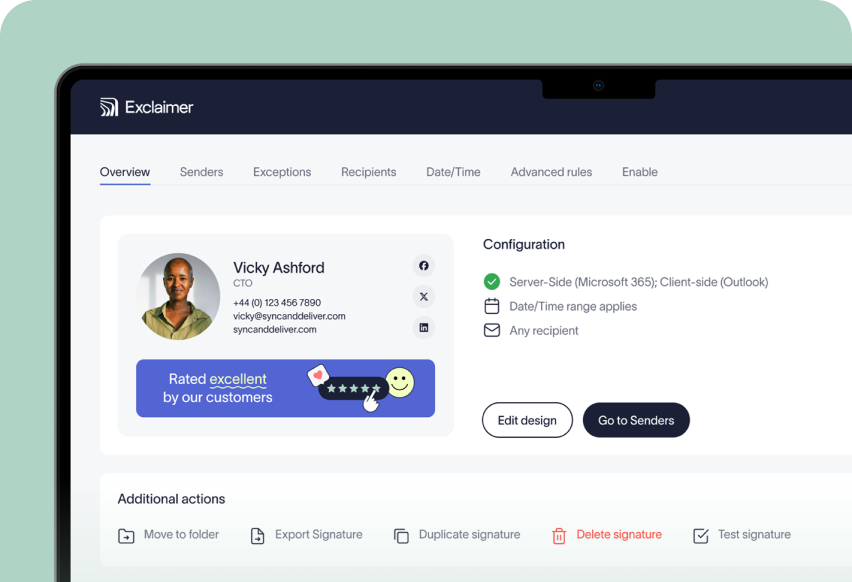
Exclaimer provides two primary deployment models: server-side processing and client-side processing.
Server-Side Processing (Mail Flow Architecture)
In server-side deployments, customer emails are routed to Exclaimer via a customer-configured mail flow rule within the customer’s email platform.
Under this model:
emails are securely transmitted to Exclaimer for processing in transit
the message is processed solely for the purpose of applying centrally managed signatures and disclaimers
the processed email is returned to the customer’s mail environment as part of normal mail flow
Exclaimer does not persistently store email message content (including email bodies or attachments) as part of routine service operation.
Exclaimer does not:
archive customer email messages
maintain historical copies of processed messages
provide any facility within the service for personnel to browse, search, or review customer email bodies
Email content is processed only to the extent technically necessary to apply configured signatures or routing logic and is not retained following processing as part of normal operations.
If access to email content is required to address a specific support request, such access will occur only where the customer has explicitly provided the content or granted express permission for that purpose.
Client-Side Processing (Outlook Add-In)
In client-side deployments (e.g., Outlook Add-in):
signature rendering occurs locally within the user’s email client
the email body remains within the customer’s environment
Exclaimer does not receive, process, or transmit the email body
Exclaimer has no access to the content of the email message
Under this model, Exclaimer processes only the configuration and directory data necessary to render the signature.
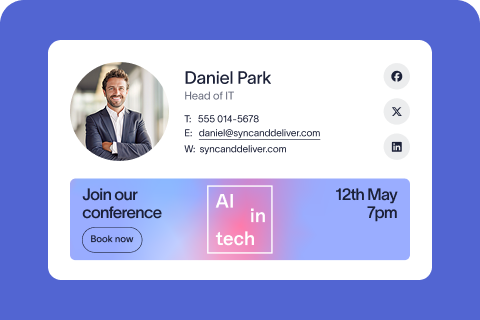
Data Stored by Exclaimer
Exclaimer stores only the data necessary to configure, administer, and operate the Services. This may include:
signature templates and rule configurations
customer tenant configuration settings
directory attributes synchronised from the customer’s email platform (e.g., name, job title, department, business contact details)
administrative account information
service metadata and operational logs
support case information provided by the customer
Data Not Stored by Exclaimer
As part of normal service operation, Exclaimer does not store:
customer email inboxes
full email bodies
email attachments
historical message archives
Access Controls Over Stored Data
Where configuration data, directory attributes, logs, or support information are stored:
access is restricted according to role-based access controls and least-privilege principles
administrative access is logged and monitored
access for support purposes is controlled and limited to authorised personnel
4. Access Control and Identity Management
Role-Based Access
Access to systems processing Customer Data is restricted on a least-privilege basis and aligned to defined role responsibilities.
Authentication Controls
Multi-factor authentication (MFA) is enforced for administrative and privileged access
Strong authentication controls are implemented for production systems
Provisioning and Deprovisioning
User access is subject to formal approval procedures. Access rights are reviewed periodically and removed promptly upon role change or termination.
Privileged Access Management
Privileged access is restricted, monitored, and subject to enhanced oversight and logging.
Logical Segregation
Logical controls are implemented to prevent unauthorised cross-customer access to data.
5. Data Confidentiality and Encryption
Encryption in Transit
Customer Data is encrypted in transit using industry-standard TLS encryption.
Encryption at Rest
Where Customer Data is stored, encryption at rest is implemented using strong cryptographic standards.
Cryptographic Governance
Cryptographic controls and key management practices are governed by documented policies aligned to recognised industry standards.
6. Availability, Resilience, and Business Continuity
Infrastructure Resilience
The Services are hosted in secure cloud infrastructure environments designed for high availability, resilience, and redundancy.
Redundancy and Failover
Systems are architected with redundancy and failover capabilities to minimise service disruption.
Business Continuity and Disaster Recovery
Documented Business Continuity and Disaster Recovery Plans are maintained, reviewed, and tested periodically.
Monitoring
Availability, performance, and security events are continuously monitored with defined escalation procedures.
7. Incident Detection and Response
Incident Management Framework
Exclaimer maintains documented incident management and information breach procedures.
Detection and Logging
Security monitoring, logging, and alerting mechanisms are implemented to detect unauthorised or anomalous activity.
Response and Containment
Security incidents are investigated, contained, remediated, and documented in accordance with formal procedures.
Breach Notification
Where required by applicable law or contract, Exclaimer will notify the Controller of a confirmed Personal Data Breach without undue delay.
8. Vulnerability and Change Management
Secure Development Practices
Secure development practices govern system design, code review, testing, and release management.
Change Management
Changes to production systems are subject to documented testing, approval, and rollback procedures.
Vulnerability Management
Regular vulnerability scanning is performed. Security patches are applied according to risk-based prioritisation. Independent security testing is conducted periodically.
9. Supplier Security and Due Diligence
Due Diligence
Exclaimer conducts appropriate security and data protection due diligence prior to engaging suppliers that may process Customer Data.
Contractual Safeguards
Suppliers processing Customer Data are subject to written agreements imposing confidentiality, security, and data protection obligations consistent with applicable law.
Ongoing Oversight
Suppliers are subject to periodic review to ensure continued compliance with security and data protection requirements.
10. Employee Security and Awareness
Background Screening
Pre-employment screening is conducted where permitted by law.
Security Training
Employees receive regular training covering information security, compliance and data protection. Training records are maintained within a learning management system.
Confidentiality
Employees are bound by confidentiality obligations as a condition of employment.
Disciplinary
Defined processes to manage violations of Exclaimer policies.
Reviews
Exclaimer maintains processes for internal audit, management review, corrective action, and improvement in alignment with its certified ISMS and independent audit requirements.