Exclaimer re-certified for ISO 27001, ISO 27018 and SOC 2 Type II
19 February 2026
0 min read
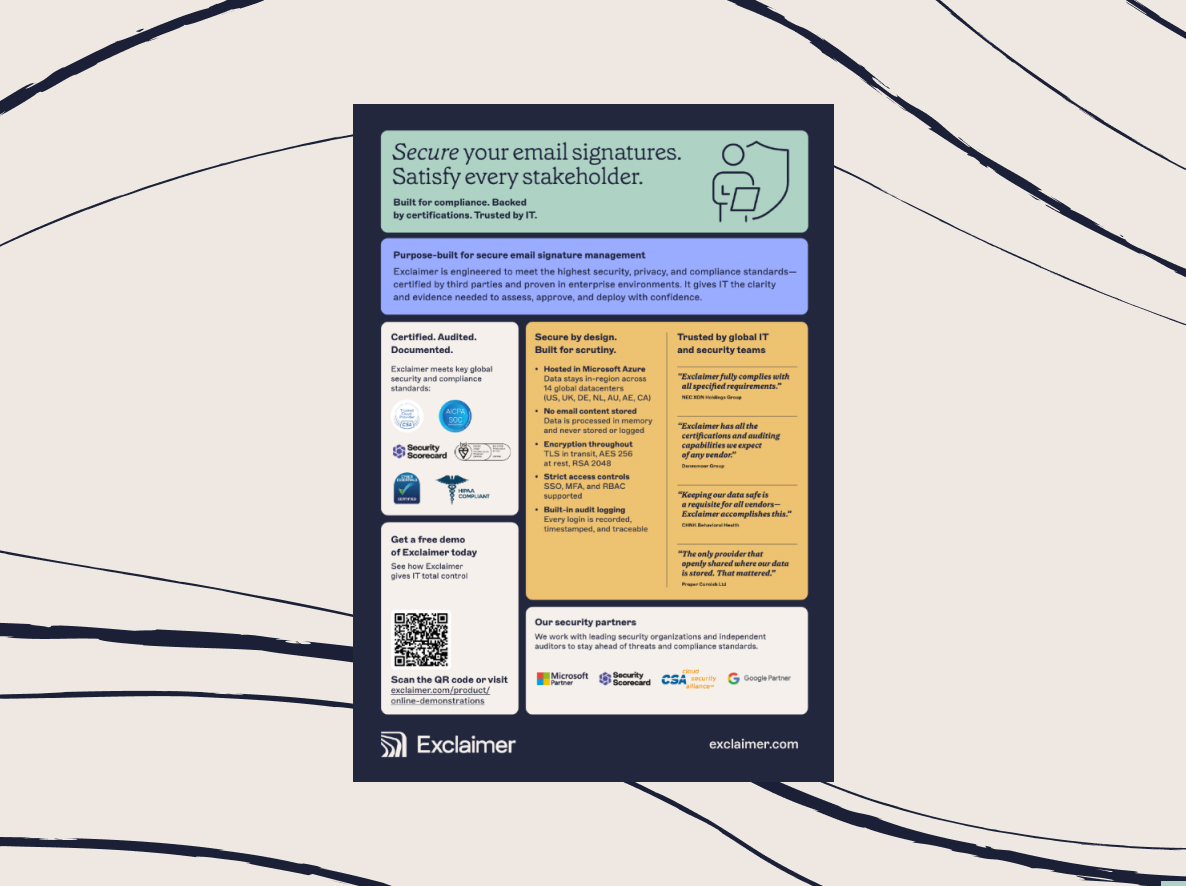
We’re thrilled to announce that Exclaimer has once again successfully passed its recent ISO/IEC 27001, ISO/IEC 27018, and SOC 2 Type II audits. These certifications confirm that our security controls, data protection practices, and governance processes have been independently reviewed and validated against internationally recognized standards.
Exclaimer is the only dedicated email signature management provider publicly listing both ISO and SOC 2 certifications. That combination matters when your team is responsible for approving SaaS tools that sit inside core communication systems.
Below, we explain why email signature management belongs within your security scope, what each certification covers in practice, and how these standards simplify vendor selection.
To see all of our security accreditations, visit the Exclaimer Trust Center. It includes summaries, certificates, reports, policy documents, and answers to over 350 security and compliance questions.
Why email signature management matters for security and compliance
Email signatures are applied to every outbound message your organization sends. That alone gives them operational reach.
From a security and compliance perspective, the impact goes further.
They process directory data
Modern email signature platforms integrate directly with Microsoft 365 or Google Workspace. They sync user attributes such as:
Full name
Job title
Department
Phone number
Office location
Custom directory fields
Much of this qualifies as personally identifiable information (PII). Any SaaS tool that processes it must meet enterprise standards for data protection, access control, and auditability.
They sit inside the corporate email flow
Signature management solutions operate either server-side or client-side. In both cases, they interact with live corporate email traffic.
That makes email signatures part of your communication surface area. If improperly secured, they could introduce risk across:
Data exposure
Incorrect or missing disclaimers
Policy inconsistencies
Unauthorized template changes
Secure email signature management reduces this exposure by embedding governance directly into outbound email.
They are reviewed during audits and vendor assessments
During ISO audits, SOC reviews, or enterprise customer due diligence exercises, vendors connected to email systems are frequently scrutinized.
Security teams must demonstrate:
Formal vendor risk assessments
Evidence of independent certifications
Ongoing monitoring and review
Without recognized certifications, reviews become more manual, more time-consuming, and harder to defend.
What ISO/IEC 27001 covers in practice
ISO/IEC 27001 is the global standard for information security management systems. It’s widely used by enterprises to assess SaaS vendor risk.
Unlike feature-level claims, ISO/IEC 27001 certifies the presence of a structured information security management system, or ISMS.
Formal security governance
ISO/IEC 27001 requires organizations to implement and maintain:
Documented security policies
Structured risk assessments
Access control frameworks
Incident response procedures
Ongoing internal review mechanisms
Security is embedded into management processes, not treated as an add-on.
Continuous improvement and audit validation
Certification is not a one-time event. Providers must:
Regularly reassess risk
Update controls as threats evolve
Undergo recurring external audits
For IT teams, ISO/IEC 27001 signals long-term commitment to security governance rather than isolated controls. As the first email signature solution to receive ISO 27001 certification, Exclaimer has been at the forefront of secure email signature management since 2016.
What ISO/IEC 27018 adds for SaaS providers
ISO/IEC 27018 builds on ISO/IEC 27001 and focuses specifically on protecting personally identifiable information in public cloud environments.
For SaaS platforms that rely on directory data, this distinction is critical.
Protection of PII in the cloud
ISO/IEC 27018 defines requirements around:
How customer data can be processed
Restrictions on secondary use of data
Access controls for cloud-hosted systems
Transparency in data handling practices
This is particularly relevant for email signature platforms that synchronize user attributes from Microsoft 365 or Google Workspace.
Clarity around cloud data handling responsibilities
Public cloud environments operate under shared responsibility models. ISO/IEC 27018 provides additional clarity around how customer data is protected, segregated, and accessed.
For compliance teams, this reduces ambiguity in vendor evaluations.
Why SOC 2 Type II matters to IT teams
SOC 2 Type II reports evaluate whether security controls are not only designed appropriately, but operating effectively over time.
This distinction is important during procurement and renewals, providing operational evidence rather than policy statements.
Operational effectiveness over a defined review period
A SOC 2 Type II audit looks at compliance over a set period of time, often 3–12 months. The associated report assesses controls across five trust criteria:
Security: Systems, infrastructure, and data are protected against unauthorized access, misuse, and breaches through defined controls and monitoring.
Availability: The service remains operational and accessible as agreed, with resilience measures that support reliability and uptime commitments.
Processing integrity: System processes function as intended, delivering complete, accurate, and timely outcomes without unauthorized alteration.
Confidentiality: Sensitive information is restricted to authorized parties and handled in line with defined protection standards.
Privacy: Personal data is collected, processed, stored, and protected in accordance with established privacy principles and access safeguards.
Auditors evaluate whether these controls operated as planned throughout the review period, not just whether they were documented.
Reduced back-and-forth during security questionnaires
Vendor security reviews often involve detailed questionnaires covering:
Encryption practices
Access management
Monitoring and logging
Incident response
An up-to-date SOC 2 Type II report allows vendors to provide independent audit confirmation. This reduces repetitive documentation requests and shortens approval cycles.
For IT and risk teams, that means fewer manual validation steps and clearer audit trails.
What makes Exclaimer different
Exclaimer is the only email signature management provider publicly listing both ISO and SOC 2 certifications.
This combination delivers two complementary forms of assurance:
Governance assurance through ISO
ISO/IEC 27001 and ISO/IEC 27018 confirm structured security governance and formal protection of cloud-based personal data.
Operational proof through SOC 2 Type II
SOC 2 Type II confirms that those controls are operating effectively over time.
Together, these certifications provide both management system oversight and operational validation. For IT teams responsible for vendor approval, this reduces uncertainty during evaluation.
What this means during vendor selection
Independent certifications have practical implications inside procurement workflows:
Faster security approvals
Recognized certifications reduce the need for evidence-gathering. Procurement teams can rely on third-party audit reports instead of vendor assertions.
Fewer exceptions or compensating controls
When vendors lack formal certifications, security teams often introduce additional contractual clauses or technical safeguards to manage risk. Certified providers reduce that need.
Lower long-term risk exposure
Ongoing audit requirements create accountability, as certifications must be maintained and revalidated. This reduces the risk of security drift over time.
Clear audit trail for internal and external reviewers
During regulatory inspections or customer due diligence exercises, documented certifications provide defensible evidence of vendor oversight.
How Exclaimer supports ongoing compliance
Passing ISO and SOC audits is a baseline. Exclaimer maintains alignment with these standards through ongoing oversight and clear documentation that supports vendor assessments and renewals.
Public Trust Center
Exclaimer maintains a public Trust Center where IT and security teams can review current certification status and supporting documentation.
Regular audits and renewals
ISO and SOC certifications require recurring external audits. Exclaimer undergoes regular assessments to maintain compliance.
Transparent documentation for security teams
IT, security, and compliance teams can access structured documentation to support vendor risk assessments and annual reviews.