The top tech trends that will shape IT in 2026
11 December 2025
0 min read
IT environments are changing quickly as we move into 2026. Identity attacks are rising. AI is now embedded in most SaaS tools. Integrations are multiplying across the stack, often faster than teams can track. The risks themselves aren’t new, but they’re harder to see because the tools enabling them look more capable than ever.
These patterns match what Exclaimer sees across the organizations we work with. Authentication is still treated like a perimeter. Vendor attestations are still read as proof of security. Annual training is still viewed as a reliable defense. In 2026, none of these assumptions will hold.
As channels expand and automation becomes routine, organizations will need tighter control over how identity is represented and governed. The trends that follow outline where IT teams will need clearer trust signals, stronger oversight, and better visibility to stay ahead.
1. Authentication will stop functioning as the perimeter in 2026
Identity has become the easiest place for attackers to get in. Valid credentials, stolen tokens, and hijacked sessions give them access that perimeter tools were never designed to stop. HYPR highlights this shift, noting that identity now defines the real security boundary.
Academic research reinforces the need for change. A study in Computers found that continuous authentication techniques outperform one-time checks in environments where credential theft is common.
In 2026, authentication will need to function as a constant handshake, not a single login event. Most organizations still rely on point-in-time verification, which leaves gaps long after a user signs in. The strength of business communication—and the trust behind it—will depend on how quickly IT teams adapt to continuous identity assurance.
2. AI inside SaaS will break the shared responsibility model
AI features inside SaaS platforms blur the boundaries of the shared responsibility model. Vendors now use third-party models to process emails, summarize CRM data, and automate decisions, often without clear visibility into how that data is handled.
This creates both security and compliance gaps. GDPR’s Article 22 and the EU AI Act require auditability for automated decisions, but many organizations can’t show how their AI systems reach conclusions. With no traceable decision path, they won’t know how their data is being used until enforcement arrives.
Palo Alto Networks’ 2026 cybersecurity predictions report notes that autonomous AI agents may outnumber human workers by 82 to 1. That shift reshapes how identity and trust need to be managed across enterprise systems. The same report found that 84% of major incidents led to downtime, brand damage, or financial loss.
When AI sits inside SaaS platforms, both vendors and customers will need clearer guardrails around data handling and accountability or risk exposure they never saw coming.
3. OAuth sprawl will become a major supply chain blind spot
OAuth connections and API integrations grow faster than most IT teams can track. Each one creates a trust relationship, and over time those permissions form a supply chain many organizations can’t fully see.
BeyondTrust’s 2026 analysis shows why this is a problem. Third-party integrations are still one of the fastest-growing causes of enterprise breaches. This is especially true when organizations can’t see which apps have access to sensitive data.
This creates a straightforward risk. When a vendor is breached, IT may not know that the vendor still has active access. OAuth tokens often stay valid for months or years unless someone removes them, giving attackers a direct path into email, identity, or communication systems.
In 2026, the real risk isn’t how many tools an organization uses. It’s how many connections no one is watching.
4. Annual security training will lose effectiveness
Annual security training will no longer reflect how modern threats work. Attackers move fast. A once-a-year session does not. So, effective training will need to be continuous and tied to real work in 2026.
PwC’s 2026 Digital Trust Insights report shows this shift clearly. More than 53% of organizations are now prioritizing AI and machine learning to close capability gaps, which signals how quickly static, point-in-time defenses are losing relevance.
The issue is straightforward. Annual training checks a compliance box, but it rarely changes behavior. People forget the content, and attackers take advantage of that gap.
5. Vendor risk assessments won’t reflect real risk
Vendor questionnaires still dominate third-party security reviews, but they won’t longer reflect how vendors actually operate in 2026. A form completed once a year can’t keep up with changes in infrastructure, subprocessors, or the way new AI features handle customer data.
As identity threats rise, this gap grows. Crowdfund Insider highlights Microsoft’s warning of a 32% increase in identity-related attacks expected in 2026. This is a reminder that threats evolve far faster than point-in-time assessments.
The result is false confidence. A vendor approved 18 months ago may now have new access paths, new dependencies, or new vulnerabilities no one is watching. Many organizations only notice these gaps after a breach is disclosed.
In 2026, point-in-time reviews will need to give way to continuous monitoring. Without ongoing visibility, vendor assurance becomes guesswork.
6. Identity visibility will become essential for fast incident response
Most breaches now start with identity misuse, not a broken firewall. Attackers use valid credentials, escalate privileges, and move through systems that aren’t monitored closely enough. By the time an alert fires, the compromised identity may already be three steps ahead.
In 2026, identity visibility will become core infrastructure. Real response time depends on it. Identity and threat signals often sit in separate tools, which means suspicious behavior goes unnoticed until logs are stitched together after the fact. CyberArk’s analysis shows that nearly three-quarters of breaches involve human error. This makes clear that attackers won’t need to break authentication when they can quietly abuse existing credentials.
But this goes beyond detection. For high-risk actions, verifying intent through a separate, trusted channel becomes standard practice. Out-of-band checks, like confirming payment changes or access requests through a known contact method, close the gap when email or identity signals aren’t enough.
Without a unified view of sessions, token activity, privilege changes, and lateral movement, teams can’t reconstruct what happened in time to contain an attack.
7. Containment will replace prevention as the dominant strategy
Trend Micro predicts that 2026 will be the year cybercrime becomes fully automated. AI agents will scan for weaknesses, exploit them, and monetize access without human involvement, running intrusion campaigns end to end.
Automation changes the tempo. Malware rewrites itself. Intrusions adapt in real time. Ransomware groups are testing “extortion bots” that identify targets and handle negotiations. Hybrid cloud environments and software supply chains sit at the top of the target list.
When attacks operate at machine speed, prevention alone can’t keep up. Containment becomes the practical strategy—isolating suspicious activity early, limiting how far attackers can move, and assuming compromise until proven otherwise.
8. Business content will become an attack surface for AI systems
In 2026, anything an AI system can read will become part of your executable attack surface. AI now reads email, scans CRM entries, and drafts responses, which means the text moving through these systems can be used against them.
OWASP warns that prompt injection allows attackers to hide instructions inside normal-looking content, causing an AI model to ignore safeguards or perform unintended actions.
This changes the threat model. A simple reply, meeting note, or support ticket can push an AI system to reveal information, summarize data incorrectly, or reroute content. And all without touching the underlying infrastructure.
Traditional filters weren’t built for this. They can flag malicious files, but not a sentence crafted to manipulate an AI model. And as organizations automate more communication, the volume of unreviewed content grows.
9. Shadow AI will emerge as a significant data leak risk
Shadow IT will be overtaken by Shadow AI in 2026. Employees are already using AI tools no one approved and no one is monitoring. Deloitte reported back in 2023 that 60 percent of employees use AI at work without informing IT, which means corporate data is flowing into systems the organization doesn’t control.
People choose whatever tool helps them work faster, even if that means pasting sensitive content into public AI models or using browser extensions that read everything on a page. When these tools operate outside IT oversight, the organization loses visibility into where its data goes and who has access to it.
Companies that want to reduce this risk in 2026 will need to offer approved AI tools that people want to use. If they don’t, employees will keep turning to unsanctioned ones.
10. Trust will shift toward verifiable communication signals
As AI generates convincing messages across every channel, trust shifts away from the words themselves and toward the signals that prove who sent them. DigiCert reports that 47 percent of organizations experienced a digital trust incident in the past two years, showing how often teams can no longer rely on message content to judge legitimacy.
Authentication becomes the anchor. Standards like DMARC, DKIM, SPF, and BIMI help confirm identity even when an attacker can replicate the text perfectly. But verification can no longer stop at email. As more communication happens in Teams, Slack, and other chat platforms without the same compliance controls, organizations will need consistent trust signals everywhere employees communicate.
In 2026, reliable communication depends on whether the sender can be verified — not whether the message “sounds right.”
Turning these trends into action
The trends shaping 2026 point to the same reality. Identity, trust, and communication now carry more risk and operational weight than before. AI accelerates both productivity and exposure, and attackers are moving through systems once considered low risk. IT teams need clearer visibility and stronger control across every channel employees use each day.
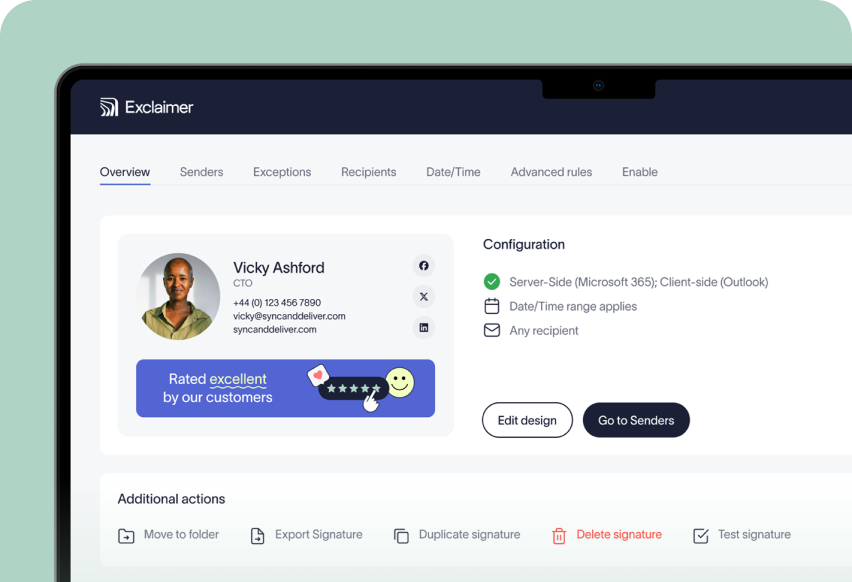
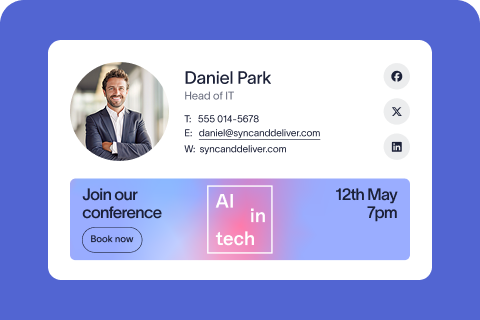
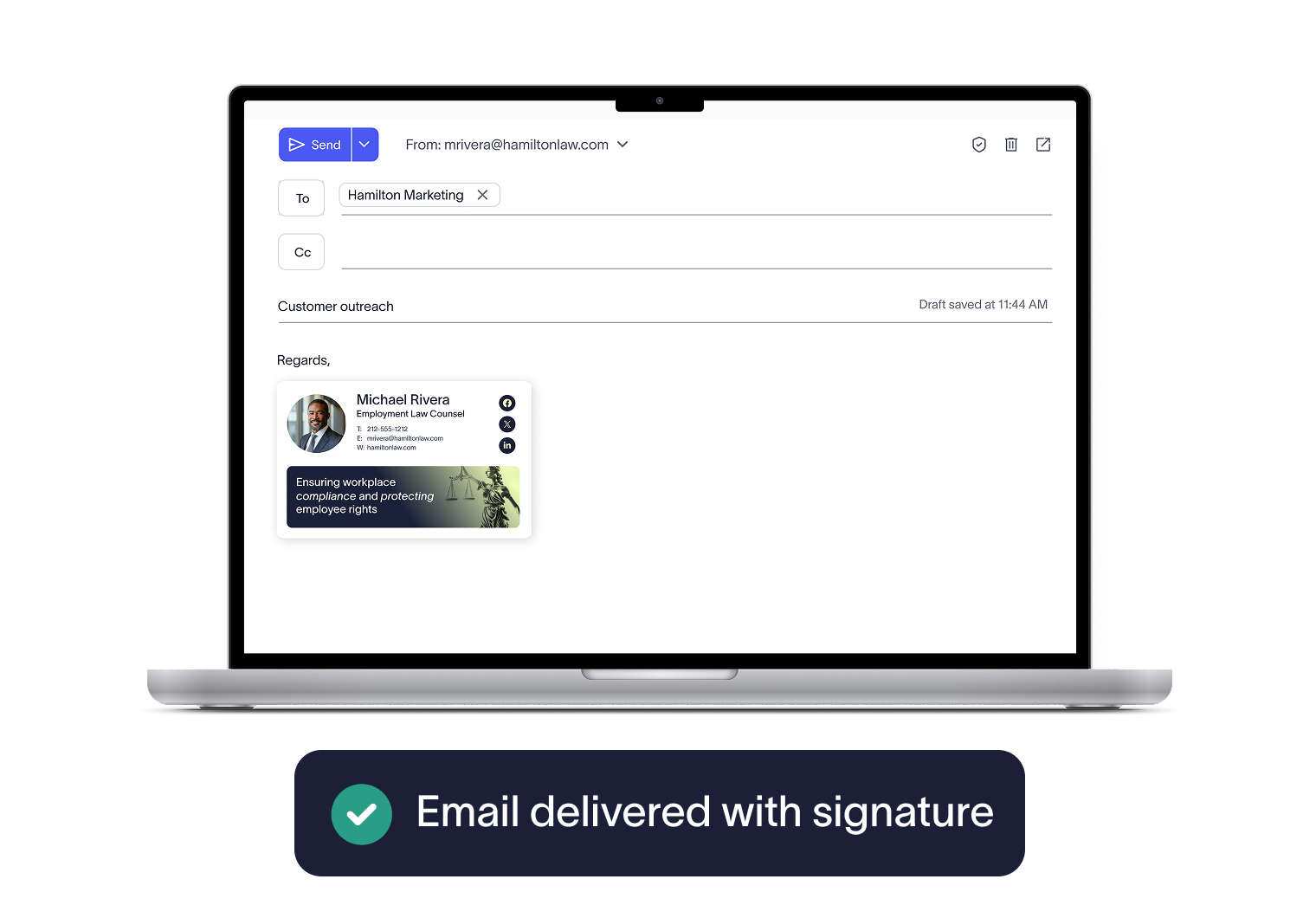
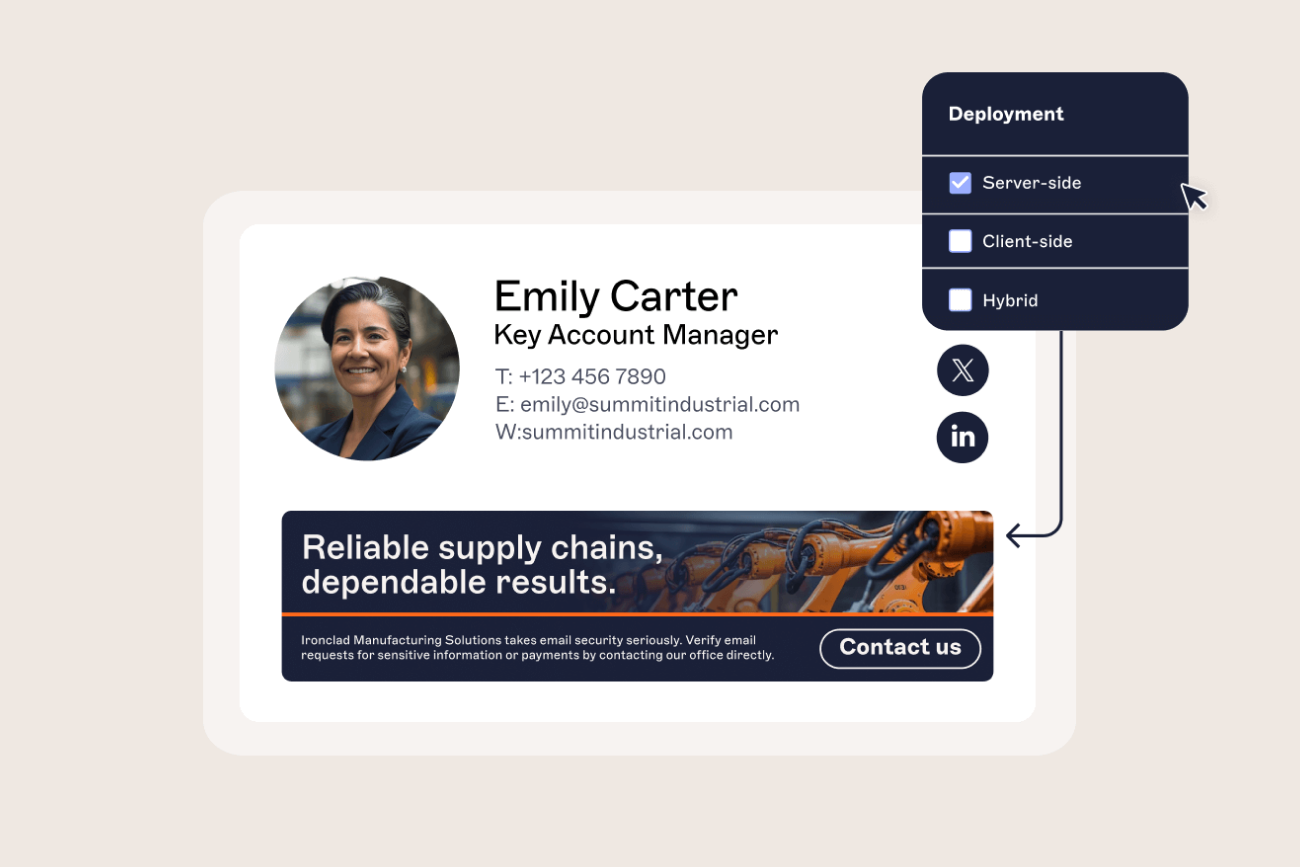
Email remains one of those channels. It is still the most reliable place to verify identity, communicate policies, and create a consistent experience. Exclaimer helps IT teams govern that layer with confidence. Our platform centralizes email signature management, enforces consistent branding and authentication signals, removing the manual work that slows teams down.
Start a free trial or book a demo to see how we can help you strengthen your communication layer for 2026.