World Cloud Security Day: What happens after “send”?
31 March 2026
0 min read
World Cloud Security Day is a good prompt to review how well your cloud environment is protected.
Most teams will focus on access. Who can log in, what they can reach, and how identities are managed across systems.
That work matters. It’s also where most of the progress has been. But it leaves a gap.
What happens after a user hits send?
The shift from access to communication risk
Cloud security has matured around controlling access. Identity, authentication, and device policies are well understood and widely implemented.
What’s less controlled is what users do once they’re inside.
“Most organizations have gotten very good at controlling who gets into their systems, but far fewer are controlling what comes out,” said Karl Bagci, Director of IT and Information Security at Exclaimer.
This is where risk is shifting—away from infrastructure, and toward how people communicate. Email sits at the center of that shift.
Email is critical and still under-governed
Email remains the system of record for business communication. Contracts, approvals, customer conversations, and compliance-related messages all pass through it.
That makes it high value, but also high risk.
83% of organizations report issues tied to email misuse, inconsistency, or risk
Only 41% have fully integrated email into their security and compliance stack
The average data breach now costs $10.22 million and takes months to detect and contain
Most teams know email matters. The issue isn’t so much awareness, but control.
Managing email signatures and disclaimers shows why. It sounds simple, but at scale, it becomes a constant source of manual work, inconsistency, and risk for IT.
Where governance breaks down
Control tends to fail at the point of execution.
That’s where emails are written and sent by individuals across different devices, locations, and tools. It’s also where policies rely on users to follow rules.
In practice, that leads to gaps:
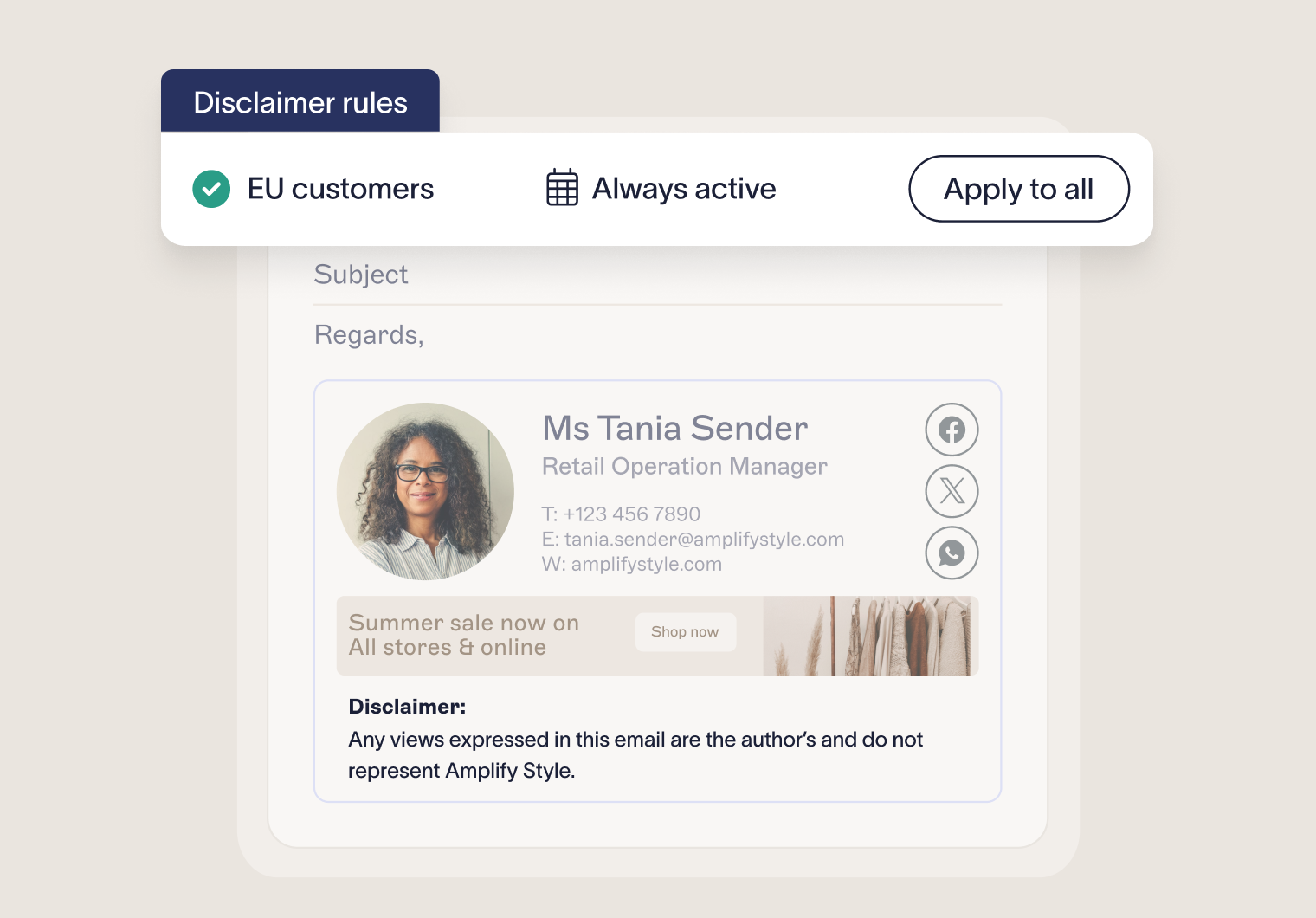
Disclaimers missing or applied inconsistently
Branding that varies across teams
Outdated or incorrect sender details
No clear audit trail of changes
These aren’t rare issues. They show up every day, especially in larger or distributed organizations.
Without centralized control, IT teams have limited visibility into how outbound communication actually looks once it leaves the business.
The hidden risk: a lack of visibility
When email isn’t part of the broader governance model, it creates a blind spot.
“This creates a critical blind spot at the point where communication exits the organization, affecting compliance, brand integrity, and customer trust,” said Bagci.
That blind spot carries real consequences.
In regulated industries, missing or inconsistent information can lead to compliance failures. In any industry, inconsistent communication can erode trust with customers and partners.
And once an email is sent, there’s no easy way to take it back.
Scale and AI are making the problem harder
The challenge isn’t static. It’s growing.
Organizations are sending more emails, across more devices, with more distributed teams. Communication is no longer confined to a single environment or controlled workflow.
AI is changing this space rapidly. Messages are drafted faster, reused more often, and generated with less oversight. At the same time, it’s enabling more intentional threats: IBM’s research shows that one in six breaches now involves AI-driven attacks.
At that scale, governance can’t depend on manual effort or user behavior. It has to be applied automatically, every time.
What real control looks like
If access control is about who gets in, communication governance is about what goes out.
For email, that means:
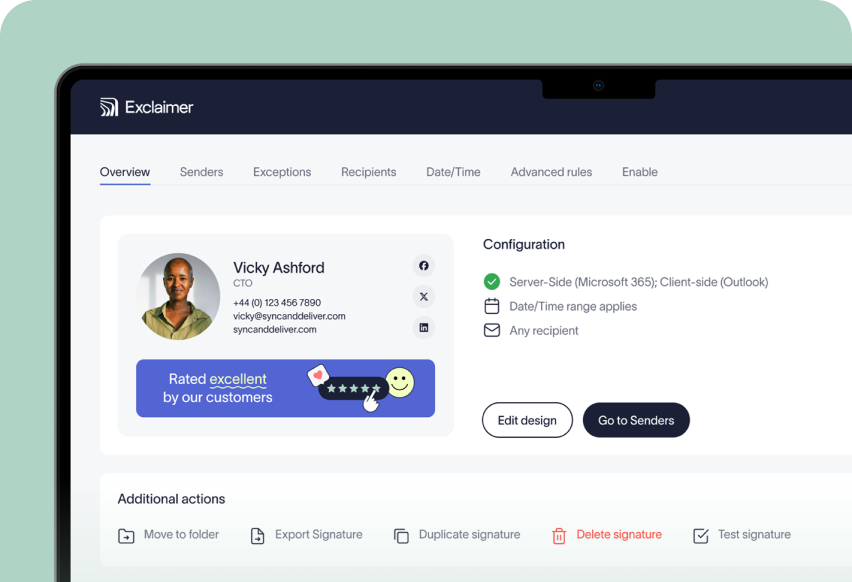
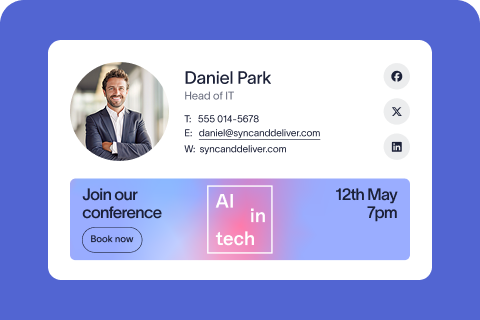
Centralized control over signatures, disclaimers, and formatting
Policy-based rules that apply automatically across all users
Real-time updates without relying on employees
Audit logs that show what was sent and when
This is the same level of control IT teams expect from the rest of their environment. It just hasn’t always been applied to communication.
Centralized email signature management is one practical way to close that gap. It gives IT a single place to manage how every email leaves the organization, without adding to their workload.
Security is about the flow of information
World Cloud Security Day is often framed around protecting systems. That’s still important. But it’s no longer enough.
“Cloud security is no longer just about protecting systems. It is about managing the flow of information across them,” said Bagci.
Every email is part of that flow. It carries legal, operational, and brand risk.
If governance stops at access, risk doesn’t.
Take control of what leaves your organization
Exclaimer helps IT teams bring email into their governance model. With centralized control, automated policies, and real-time updates, every email stays consistent, compliant, and under control without manual effort.
Book a demo to see how it works in your environment.